Secrets Management stories
BeyondTrust & AWS partner to boost cloud identity security
5 days ago
#
data protection
#
hybrid cloud
#
hyperscale
BeyondTrust and AWS have teamed up in a multi-year deal to enhance cloud identity security, offering integrated solutions for safer hybrid cloud adoption.

Poor cloud security leaves secrets & data at risk, report finds
Last week
#
hyperscale
#
public cloud
#
cloud security
A report finds poor cloud security and misconfigurations put sensitive data and secrets at risk across major public cloud providers worldwide.
Codiac 2.5 boosts real-time observability & secure cluster control
This month
#
virtualisation
#
devops
#
hybrid cloud
Codiac 2.5 delivers real-time observability, zero-trust security, and centralised cluster control for containerised workloads across multi-cloud and on-premises environments.

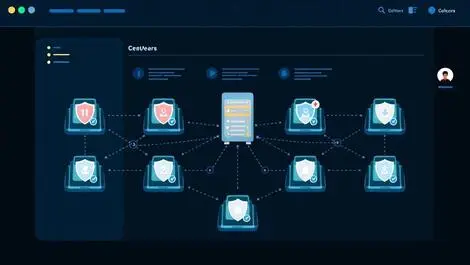
CyberArk named leader in secrets management by KuppingerCole
Last month
#
hybrid cloud
#
pam
#
cloud security
CyberArk named Overall Leader in KuppingerCole's 2025 Enterprise Secrets Management report for its AI-powered identity security platform.

Cycode unveils AI Teammates & real-time runtime protection
Thu, 24th Apr 2025
#
application security
#
advanced persistent threat protection
#
devsecops
Cycode launches AI Teammates and CI/MON runtime protection to enhance software supply chain security and threat detection in application security.

CyberArk launches new machine identity security solution
Fri, 11th Apr 2025
#
virtualisation
#
cloud security
#
open source
CyberArk has launched its Secure Workload Access Solution to bolster machine identity security, enhancing protections against credential-based attacks in hybrid environments.

GitHub Action compromise affects over 23,000 repositories
Thu, 20th Mar 2025
#
supply chain
#
open source
#
software development
A malicious commit in the tj-actions/changed-files GitHub Action, used in over 23,000 repositories, threatens software security across numerous CI pipelines.

Venafi launches SaaS machine identity products in Australia
Mon, 3rd Mar 2025
#
saas
#
virtualisation
#
hybrid cloud
Venafi has launched its cloud-based machine identity security solutions in Australia, enhancing organisations' ability to manage risks as AI adoption rises.

Carlsberg enhances development with GitHub integration
Wed, 15th Jan 2025
#
devops
#
digital transformation
#
apm
Carlsberg has enhanced its development processes by integrating GitHub's tools, streamlining coding and security while reducing operational tool sprawl.

30,000 Postman workspaces leak API keys & credentials
Fri, 27th Dec 2024
#
phishing
#
martech
#
email security
CloudSEK has uncovered over 30,000 exposed Postman workspaces leaking sensitive API keys, affecting major firms across healthcare, finance, and sports sectors.

GitGuardian unveils strategy to protect non-human identities
Wed, 18th Dec 2024
#
network infrastructure
#
cloud security
#
api
GitGuardian has launched a Non-Human Identity Security strategy to enhance the management of NHIs and their secrets, addressing enterprise security challenges.

GitGuardian report highlights rising secrets security concerns
Fri, 1st Nov 2024
#
application security
#
supply chain
#
cyberark
GitGuardian's 2024 report reveals that 79% of IT leaders have seen secrets leaks, highlighting growing concerns and a shift towards enhanced security measures.

Entro Security report reveals critical risks in managing NHIs
Tue, 17th Sep 2024
#
cybersecurity
#
security vulnerabilities
#
secrets management
Report reveals grave cybersecurity flaws, with 97% of Non-Human Identities having excessive privileges and 44% of tokens exposed.

Survey reveals security gaps in managing non-human identities
Tue, 17th Sep 2024
#
pam
#
cloud security
#
iam
A survey reveals critical security gaps in managing non-human identities, with only 15% of organisations confident in their NHI security measures.

Entrust launches KCaaS, enhancing cloud-based key management
Fri, 23rd Aug 2024
#
virtualisation
#
encryption
#
veeam
Entrust unveils KeyControl as a Service, addressing critical gaps in key management with its cloud-based solution, enhancing security and compliance.

Tessell partners with HashiCorp to enhance DBaaS features
Fri, 14th Jun 2024
#
encryption
#
microsoft
#
cloud services
Tessell partners with HashiCorp to boost its DBaaS platform by integrating automation and security tools, enhancing flexibility, scalability, and security for users.

Avocado Consulting expands partnership with CyberArk
Mon, 15th Apr 2024
#
virtualisation
#
devops
#
digital transformation
Avocado, a consulting firm, has announced an enhanced partnership with CyberArk to bolster identity security in Aussie and Kiwi firms amidst swift digital transformation.

Leaked secrets on GitHub rose by 28% in 2023, report reveals
Thu, 14th Mar 2024
#
it training
#
data privacy
#
cybersecurity
The 2024 State of Secrets Sprawl report reveals a 28% rise in new secret occurrences leaked on GitHub in 2023, exposing a significant security gap and putting various sectors at risk.

GitGuardian & CyberArk partner for secrets security solution
Fri, 9th Feb 2024
#
devops
#
apm
#
software development
Secrets detection specialist GitGuardian collaborates with CyberArk to tackle Secrets Sprawl in DevOps, offering automated detection and leak remediation.

GitGuardian launches free toolset to protect business secrets
Fri, 20th Oct 2023
#
supply chain
#
apm
#
cybersecurity
GitGuardian has launched 'HasMySecretLeaked,' a tool to help security engineers check if their organisation's secrets have leaked on GitHub.